Automate Safely, Build Freely
Today we dive into privacy-conscious no-code automations built around local triggers and minimal data sharing, so your routines move fast without exporting your life. Expect practical patterns, honest lessons, and tools that keep decisions on your devices, reduce exposure by default, and still deliver delightful time savings for solo builders, small teams, and privacy-first organizations.
On-Device Schedules and Sensors
Timers, clipboard watchers, Bluetooth proximity, and battery thresholds can cue routines precisely when they matter, without leaking identifiers to remote services. Think of a morning focus script that silences notifications, opens drafts, and rotates wallpapers locally, proving that personal ambience and productivity can synchronize seamlessly while private state remains yours alone.
Network Boundaries and Air-Gapped Cues
Triggering from a NAS file drop, a home gateway ping, or a USB key insertion keeps execution anchored where you control logs and access. Even partial air-gaps help: a laptop listens on localhost, processes payloads offline, and exports only derived, redacted summaries when absolutely needed and explicitly approved by you.
Human-in-the-Loop Confirmations
A subtle desktop prompt or mobile approval widget adds consent at the decisive moment. Instead of blind automation, you validate context, preview redactions, and apply a one-tap override. These micro-pauses transform risky moments into confident choices, preserving speed while honoring boundaries your future self will appreciate and trust.
Build Without Handing Over Your Life: Tooling That Respects Boundaries
You can assemble powerful workflows using tools that prioritize control over convenience theater. Self-hostable orchestrators, local-first mobile shortcuts, and privacy-aware home platforms let you compose actions like blocks, while secrets stay on your disk, logs remain yours, and integrations are added intentionally, not accidentally exposing identity crumbs with every scheduled run.
Self-Hosted Flows with n8n or Node-RED
Running automation servers on your machine or private VPS ensures configuration, credentials, and history never enrich third parties. Nodes can strip fields, hash identifiers, and branch conditionally before any network call. With containerization and backups, recovery is straightforward, and every outbound request becomes a deliberate, documented, and revocable choice.
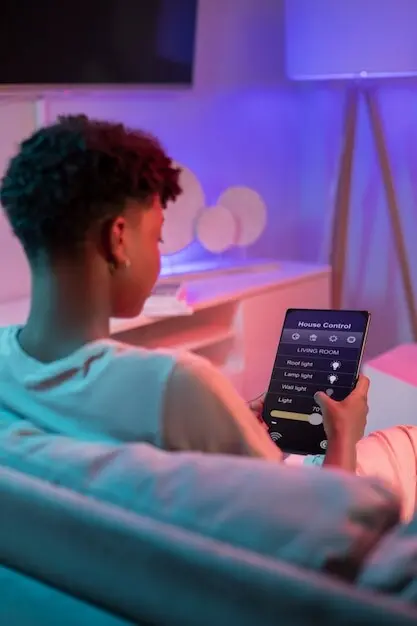
Apple Shortcuts and Android Routines as Private Launchpads
Phone-based routines already know your contexts, yet they can compute locally and store results in protected app sandboxes. Use share sheets, widgets, and NFC tags to initiate actions without spilling content. When remote services are required, send only hashes or tokens, never full messages, images, or contact details by default.
Home Assistant Automations with Local Control
A local hub unifies sensors, lights, and presence detection without mandatory cloud relays. Automations can snapshot states, derive compact signals, and actuate scenes instantly. When sharing, publish non-identifying events, not raw camera feeds or device serials. Your home remains responsive, while insight escapes only as carefully curated, reversible hints.
Data Minimization by Design: Share Less, Achieve More
A privacy-strong workflow begins by asking what can be omitted entirely. Redaction, hashing, tokenization, and summarization convert rich inputs into lean signals that still drive decisions. Instead of sending whole documents, emit counts, statuses, or anomaly flags, protecting people while preserving enough context to guide precise, confident, and reproducible outcomes.
Guardrails That Empower: Security Patterns for Everyday Makers
Protection should feel enabling, not obstructive. Scoped tokens, secret vaults, least privilege, and explicit approvals let you innovate quickly without roulette. Clear audit trails and panic stops mean experiments remain reversible. When credentials leak or a cron misbehaves, you contain blast radius gracefully, learn fast, and restore trust intentionally.
A Freelancer’s Invoice Pipeline That Never Leaves the Laptop
PDF parsing, line-item checks, and ledger updates run locally with a nightly on-device schedule. Only anonymized totals and payment statuses reach a bank API. When a client disputed hours, the builder produced redacted logs proving integrity without revealing project notes, preserving relationships while upholding boundaries that once felt impossible.
A Family Photo Workflow with Selective Cloud Sync
Cameras back up to a home server, which de-duplicates images and classifies scenes offline. Relatives receive low-resolution previews via signed, expiring links. Full originals remain encrypted at home. Sharing increased because trust improved, and no one worried that private gatherings or children’s faces might ricochet across unpredictable ad ecosystems.
A Nonprofit’s Neighborhood Alerts on a Mesh Network
Local sensors feed a self-hosted orchestrator that aggregates environmental readings into simple traffic-light statuses. Volunteers see color codes, not raw GPS trails or identities. On event days, a manual confirmation gates broadcasting. The group met compliance easily, secured grants faster, and protected communities while still mobilizing timely, verifiable action.

From Prototype to Habit: Maintainable, Trustworthy Routines
Privacy-friendly automation becomes culture when small practices compound. Document redaction rules, rehearse failure modes, version flows, and invite lightweight peer reviews. Measure usefulness with local metrics, not invasive analytics. Celebrate weekly improvements, retire brittle steps, and keep curiosity alive so your guardrails evolve alongside your ambitions, tools, and communities.